We often get asked how NetEqualizer compares to companies that do Application Shaping (aka “deep packet inspection (DPI)”, or "Layer-7" shaping). Our Comparison White Paper will clarify the differences between NetEqualizer’s behavior-based approach and the rest of the pack. Overall, equalizing is a simple concept to understand. Equalizing is the art form of looking at the usage patterns or traffic “behaviors” on the network, and then when things get congested, robbing from the rich (bandwidth hogs) to give to the poor. This behavior-based approach to traffic shaping usually mirrors what you would end up doing if you could see and identify all of the traffic on your network, but does not require the labor and cost of classifying everything. Applications such as VoIP, web-based business applications (SaaS, cloud-based apps), Internet browsing, and instant messaging (IM) all naturally receive higher priority, while large downloads and video receive lower priority. As behavior-based shaping does not care what the traffic type (aka “application”) is, it also does not need to be updated constantly as applications change.Comparison White Paper
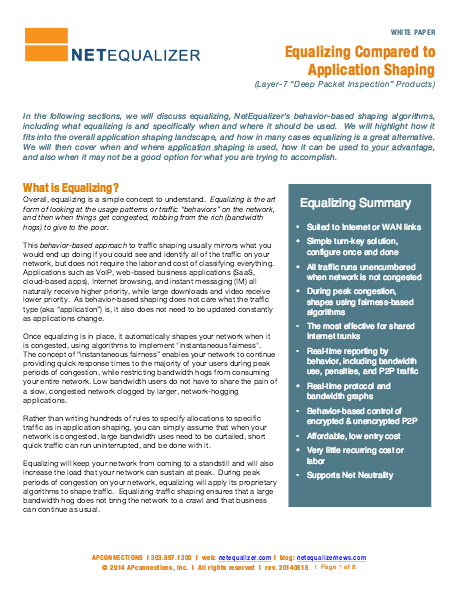
In the following sections, we will discuss equalizing, NetEqualizer's behavior-based shaping algorithms, including what equalizing is and specifically when and where it should be used. We will highlight how it fits into the overall application shaping landscape, and how in many cases equalizing is a great alternative. We will then cover when and where application shaping is used, how it can be used to your advantage, and also when it may not be a good option for what you are trying to accomplish. What is Equalizing?